Payment Proof in Kenya Moves From Contacts to Transaction Codes
A simple transaction code is doing the work that identity once carried, deciding in real time whether money is acknowledged, questioned, or lost in the gap between systems and people
On most days, the message that settles a payment is no longer a voice call, a handshake, or even a phone number. It is a string of characters. A transaction code. Increasingly, that code is enough.
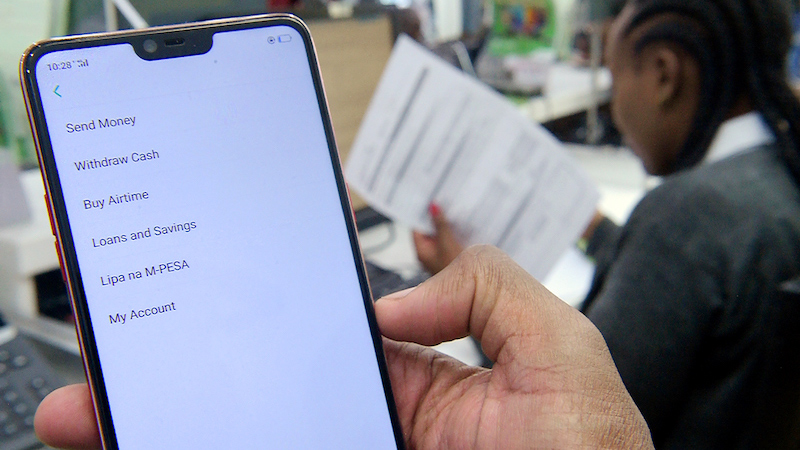
What Safaricom has done with M-PESA is subtle on the surface. Mask the phone number. Reduce the visible identity. Keep the transaction details intact. The shift is framed as privacy. It is that. But it also reorganizes how proof works in everyday life.
The transaction ID, once a backend reference, is becoming the front-facing evidence of exchange.
From identity to artifact
The earlier logic of mobile money tied proof to a person. A full name. A full phone number. A message that could be read as both confirmation and identity check. Payment and person were fused.
Data minimization breaks that fusion. The number is now partially hidden. Names are reduced. What remains fully intact is the transaction record: amount, timestamp, and the transaction code itself .
That balance is deliberate. Less identity. Same transaction integrity.
In practice, it means the center of gravity shifts. The phone number fades as a verification tool. The transaction code steps forward as the durable reference. It is not who paid that matters first. It is whether a valid transaction exists.
The transaction code as portable proof
A transaction code travels well. It does not depend on context or proximity. It can be copied, forwarded, screenshotted, archived. It survives outside the system that generated it.
This is what makes it “portable proof.”
In a rent dispute, a tenant no longer needs to argue recognition. They present a code. In a delivery handoff, a rider does not need to trust a name. They ask for the message and confirm the reference. In a chama contribution, the treasurer tracks compliance through codes submitted, not conversations held.
The code compresses the transaction into something verifiable and transferable. It becomes a unit of proof that can be carried across platforms, across time, and across informal systems.
Screenshot culture becomes financial infrastructure
This portability feeds directly into a behavior that already exists: screenshotting.
The screenshot has been casual documentation. A way to remember, to reassure, to share. With data minimization, it becomes something more structured. A financial record.
Each screenshot contains the minimum viable dataset: partial identity, full transaction details, and the transaction code. That is enough for most social and commercial interactions. Enough to confirm payment. Enough to resolve routine disputes.
People are already building personal archives. Chat threads become ledgers. Photo galleries become proof repositories. WhatsApp groups double as audit trails.
The system does not formally recognize these as records. But socially, they function as such.
Informal enforcement reorganizes around the code
Kenya’s payment ecosystem runs as much on informal enforcement as on formal systems. Landlords, small traders, chama officials, delivery riders. Each operates with lightweight verification methods that rely on speed and plausibility.
The masked number forces a recalibration.
Where a landlord once matched a full phone number to a tenant, they now rely on the transaction code and the consistency of payment patterns. Where a rider once confirmed identity through a number, they now verify against the message and code. Where a chama once tracked contributions by names and contacts, it now compiles transaction references.
The code becomes the anchor point. It is harder to fake convincingly at scale, easier to standardize in records, and simpler to request in disputes.
Even the new verification pathway—sending a transaction message to a short code like 334 to request full details—reinforces this structure. It treats the transaction itself as the starting point, not the person behind it.
Legal weight versus social acceptance
There is a gap here that has not fully closed.
Legally, a transaction code on its own sits in an ambiguous space. Formal dispute resolution still leans on system logs, provider verification, and identity linkage. A screenshot can support a claim, but it is not definitive without backend confirmation.
Socially, the threshold is lower. A valid-looking transaction message, anchored by a code, is often enough to settle matters. The burden of proof is negotiated in real time, and the code carries significant weight in that negotiation.
This divergence matters. It creates a two-tier system of proof.
In everyday transactions, the code is authoritative. In formal disputes, it is evidentiary but not final.
Over time, these layers tend to converge. As behavior standardizes around transaction codes, institutions adapt. What is socially accepted often becomes formally recognized, especially when it is already embedded in system design.
Privacy as a structural shift
The stated goal of data minimization is clear: reduce exposure, limit misuse, protect users from spam and fraud . Masking phone numbers removes a key vector for unwanted contact and social engineering.
But privacy changes structure.
By stripping away easily visible identity markers, the system forces reliance on the transaction artifact itself. It elevates the code not just as a reference, but as the primary proof.
This is not a feature users will necessarily notice immediately. Payments will still go through. Messages will still arrive. Names will still appear, albeit reduced.
What changes is what people trust.
And increasingly, what they trust is a sequence of characters that confirms a transaction happened, recorded somewhere in the system, retrievable if needed.
A new baseline for proof
Kenya’s mobile money system has always blurred the line between formal finance and everyday social exchange. The rise of the transaction code sharpens that line in a different place.
Proof is no longer anchored primarily in identity. It is anchored in verifiable events.
The transaction code is the simplest expression of that event. It is short, abstract, and system-generated. It does not tell a story on its own. But it points to one that can be verified.
That is enough.
In time, the expectation settles. If you paid, you have a code. If you cannot produce it, the payment is incomplete in the eyes of the other party.
The quiet shift is complete when that expectation becomes instinctive.
Mark your calendars! The GreenShift Sustainability Forum is back in Nairobi this August. Join innovators, policymakers & sustainability leaders for a breakfast forum as we explore sustainable solutions shaping the continent’s future. Limited slots – Get your early bird tickets now – here. Email info@techtrendsmedia.co.ke for partnership requests.
Go to TECHTRENDSKE.co.ke for more tech and business news from the African continent and across the world.
Follow us on WhatsApp, Telegram, Twitter, and Facebook, or subscribe to our weekly newsletter to ensure you don’t miss out on any future updates. Send tips to editorial@techtrendsmedia.co.ke




