A Telegram and WhatsApp Vulnerability Could Allow Attackers Manipulate Your Media Messages
Messaging platforms are popular these days and everyone other user values the privacy of their activities on these platforms. WhatsApp and Telegram have often boasted of their secure messaging solutions thanks to the implementation of the end to end encryption by both platforms.
However, Symantec a cybersecurity research group has revealed a vulnerability on these platforms could allow attackers to exploit and manipulate your media files.
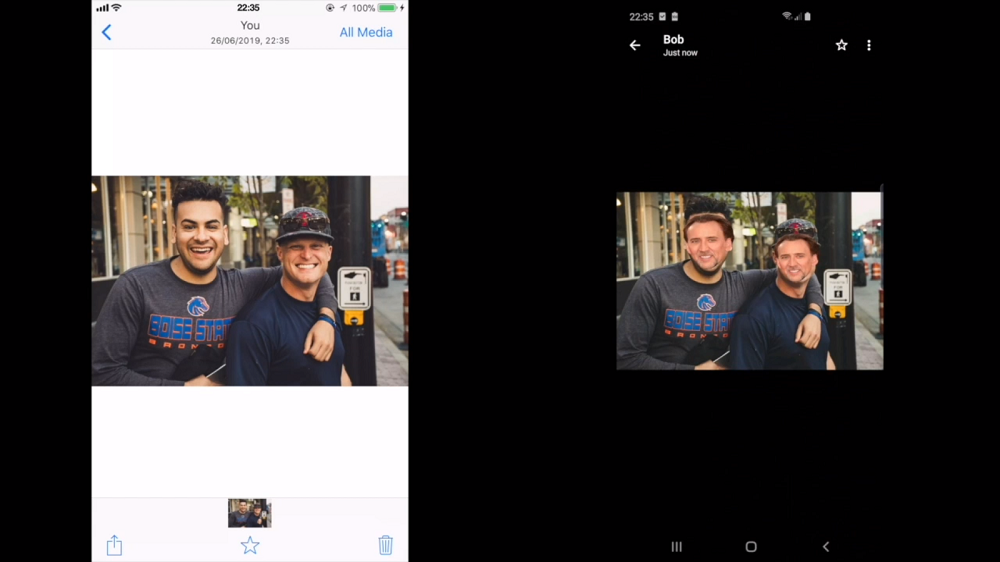
The vulnerability dubbed “Media File Jacking” originates from the point a media message is loaded into the app User interface or when a media message is received via the app. By default, WhatsApp stores media messages via external storage meaning other apps can also access the media files while Telegram stores media messages in the internal storage and can be stored externally in case you select to “Save to Gallery.”
Researchers have revealed Media File Jacking malware with access to external storage can manipulate a received message even before the receiver sees it. Similarly, the malware can also manipulate a send message moments before its send via the messaging apps.
WhatsApp, in response to the matter, stated, the app uses “the current best practices provided by operating systems for media storage and looks forward to providing updates in line with Android’s ongoing development.” Adding that the vulnerability, if tackled in the right way, could impact the user experience and even introduce more vulnerabilities in the apps ecosystem. Telegram has not responded to the matter yet.
Due to lack of ways to mitigate the Media File Jacking vulnerability, Symantec states you could stay safe by disabling the feature which allows media to be saved to the external storage. The research group notes that even if best practices are implemented, “no code is immune to security vulnerabilities.”
https://youtu.be/FHvkGUh8S_c
Follow us on Telegram, Twitter, Facebook or subscribe to our weekly newsletter to ensure you don’t miss out on any future updates.



